In this article, you will learn what two-factor authentication (2FA) is, how it works, which methods are actually secure and how to enable them correctly, especially for accounts tied to advertising, traffic monetization and payments.
Most online accounts today are protected by only a password. This is a massive risk; according to industry reports, a large share of security breaches are linked to weak, stolen or reused passwords. Once a password leaks, attackers can try it on hundreds of other services, often without the user even noticing.
Two-factor authentication (2FA) adds a second layer of protection. Even if someone gets your password, they still need a second form of verification.
It’s one of the simplest and most effective ways to secure your accounts, yet many people either don’t use it or choose weaker methods that can still be bypassed.
What is Two-Factor Authentication?
2FA is a security method that requires two different types of proof to verify your identity.
Instead of just one factor (a password), you need an additional factor (like your phone or a physical key) in order to verify your identity.
For example, you enter your password, then you enter a code from your phone. Only after both steps are completed, you get access.
The Three Pillars of Authentication
To be considered true 2FA, the two factors must come from different categories:
| Factor type | What it means | Examples |
|---|---|---|
| Something you know | Information you remember | Password, PIN |
| Something you have | A device you own | Phone, security key, authenticator app |
| Something you are | Your physical identity | Fingerprint, Face ID |
A password and a security question (e.g., "Your pet's name") are not 2FA because they both fall under information you know. If a hacker breaches a database, they can often find the answers to both.
A password alone is not enough anymore. 2FA adds a second barrier that attackers usually can’t bypass, even if they already have your login details.
2FA vs. MFA (Quick Clarification)
You’ll often see these terms:
- 2FA (two-factor authentication) → exactly 2 factors
- MFA (multi-factor authentication) → 2 or more factors
In practice, all 2FA methods are MFA, but not all MFA methods are limited to two steps.
How Two-Factor Authentication Works
The process adds one simple but powerful step to your login flow.
- Login: You enter your username and password.
- Verification: The service requests a second factor (e.g., a 6-digit code or a push notification).
- Validation: You provide the code or approve the request on your secondary device.
- Access: The system grants entry.
Most 2FA codes are TOTP (Time-based One-Time Passwords). They expire every 30–60 seconds, making them useless to hackers if intercepted after the fact.
Real-Life Example
Let’s say someone gets your password from a data leak. Without 2FA, they log in and get instant access. With 2FA, they log in, the system asks for a code, they don’t have your phone, so access is denied.
2FA links grant login access when provided with not only your password but also you and your device in real time.
Why Passwords Are No Longer Enough
For years, passwords were the gold standard. Today, they are the weakest link. Even if you use a "strong" password, you are still at risk.
- Data breaches: Services get hacked constantly. When one site leaks your password, hackers try it on hundreds of other sites (credential stuffing).
- Phishing: Sophisticated fake emails or websites can trick even tech-savvy users into typing in their credentials.
- Automated attacks: Bots can try thousands of combinations in seconds.
A password only proves that someone knows it, not that it’s actually you. Once a password is stolen, there’s nothing stopping an attacker from using it.
Types of 2FA and Which Ones Are Actually Secure
Not all 2FA methods offer the same level of protection. Some are much harder to bypass than others.
Most Secure 2FA Methods
These are the most secure and should be your first choice when available.
- Authenticator apps (Google Authenticator, Authy): Generate time-based codes directly on your device. They work offline and are hard to intercept.
- Hardware security keys (like YubiKey): Physical devices you plug in or tap. They are extremely resistant to phishing.
- Passkeys: Newer method that replaces passwords entirely using your device + biometrics or PIN.
For most people, authenticator apps are the easiest and most practical option. If you want the highest level of security, hardware keys or passkeys are the better choice.
Good but Not Perfect 2FA Methods
These are convenient and widely used; however, they do have some risks.
- Push notifications: You approve a login with one tap. It is easy to use, but can be abused with repeated requests (so-called “push fatigue”).
- Biometrics (Face ID, fingerprint): This method is fast and user-friendly, but usually tied to your device and not always a standalone factor.
Weaker 2FA Methods
These options are widely used, but they offer lower security and should only be a fallback if stronger methods aren’t available.
- SMS codes: These are common and easy to use, but they can be vulnerable to SIM-swapping attacks and interception.
- Email codes: This is the least secure option. If your email account is compromised, attackers may be able to access all your linked accounts.
| Method | Security level | Main risk |
|---|---|---|
| Hardware keys | ⭐⭐⭐⭐⭐ | Can be lost |
| Authenticator apps | ⭐⭐⭐⭐ | Device access |
| Push notifications | ⭐⭐⭐ | Approval fatigue attacks |
| SMS codes | ⭐⭐ | SIM swap |
| Email codes | ⭐ | Email compromise |
Any 2FA is better than none, but not all 2FA are equal. If you want real protection, avoid SMS when possible and use an authenticator app or stronger methods instead.
2FA Best Practices: How to Use It the Right Way
Enabling 2FA is a great first step, but using it correctly is what keeps your account safe. Here are the most important things to get right.
1. Use the Strongest Method Available
If you have a choice, avoid SMS and email codes. An authenticator app is a much safer default, and for sensitive accounts, hardware keys or passkeys provide even stronger protection.
2. Always Save Your Backup Codes
When you enable 2FA, most services give you backup (recovery) codes. Don’t ignore them. Store them somewhere safe: offline (printed or written down) or in a secure password manager. Without them, losing access to your device can lock you out of your account.
3. Protect Your Email First
Your email is often the gateway to all other accounts. If someone gets access to it, they can reset passwords and bypass security on other services. So your first priority is to enable 2FA on your email before anything else.
4. Never Approve Unexpected Requests
If you get a login prompt, code or push notification you didn’t request, don’t approve it. This could mean that someone is trying to access your account or your password has already been compromised.
5. Use Unique Passwords Even With 2fA
2FA is powerful, but it’s not a magic fix. If you reuse passwords across multiple sites, one breach can still create problems. Combine 2FA with strong, unique passwords for real protection.
6. Add a Backup Method if Possible
Many services let you add a second device, a backup phone number or an alternative verification method. This helps you avoid lockouts without weakening security.
2FA works best when you treat it as part of a system. Strong method + backup access + good habits = real protection.
What to Do If You Lose Access to 2FA
Losing access to your 2FA method can happen, for example, if you lose your phone or reset your device. The important thing is to recover access safely without compromising your account.
The Most Common Recovery Options
Most services provide backup ways to log in:
- Backup codes: Generated when you enabled 2FA
- Secondary device or method: Another phone or app
- Recovery email or phone number: Used to regain access
- Support verification: Manual identity check
This is why setting up backups in advance is so important.
If You Still Have Your Backup Codes
- Use one of your backup codes to log in.
- Go to security settings.
- Set up 2FA again on your new device.
If You Lost Everything (No Codes, No Device)
Recovery is trickier, but not impossible. You’ll need to:
- Request account recovery.
- Verify your identity (email, documents, activity, etc.).
- Wait for support to review your request.
This process can take time and isn’t always guaranteed.
How to Avoid Getting Locked Out
A few simple steps can save you a lot of trouble:
- save backup codes in a safe place;
- add a secondary 2FA method if available;
- keep your recovery email up to date.
2FA protects your account, but only if you can still access it yourself. Set up recovery options early, not when it’s already a problem.
2FA in MGID: Protecting Your Campaigns and Funds
To see how 2FA works in practice, let’s look at how it’s implemented in MGID.
The idea stays the same: access to your account requires not only a password but also a secondary verification step. For MGID, this is a one-time code (OTP) sent to your email address. This means that even if someone gets your password, they still won’t be able to access your account without also having access to your email.
The effectiveness of email-based 2FA depends on how well your email account is protected. If your email is secured (strong password + 2FA), then this setup provides a solid level of protection for your MGID account.
Why This Matters for MGID Users
For accounts connected to advertising and payments, the stakes are higher.
If you use MGID to manage campaigns, monetize traffic or handle funds, your account is directly tied to financial activity and sensitive data.
At MGID, we prioritize the safety of our clients and partners. Adding extra protection like 2FA is part of our commitment to keeping your data secure.
What Protection You Get
Enabling 2FA in MGID helps:
- reduce the risk of account breaches caused by leaked or reused passwords;
- protect campaign data and financial operations;
- add an extra barrier against unauthorized access;
- follow widely accepted security best practices.
How to Enable 2FA in MGID
You can enable 2FA in just a few steps from your dashboard.
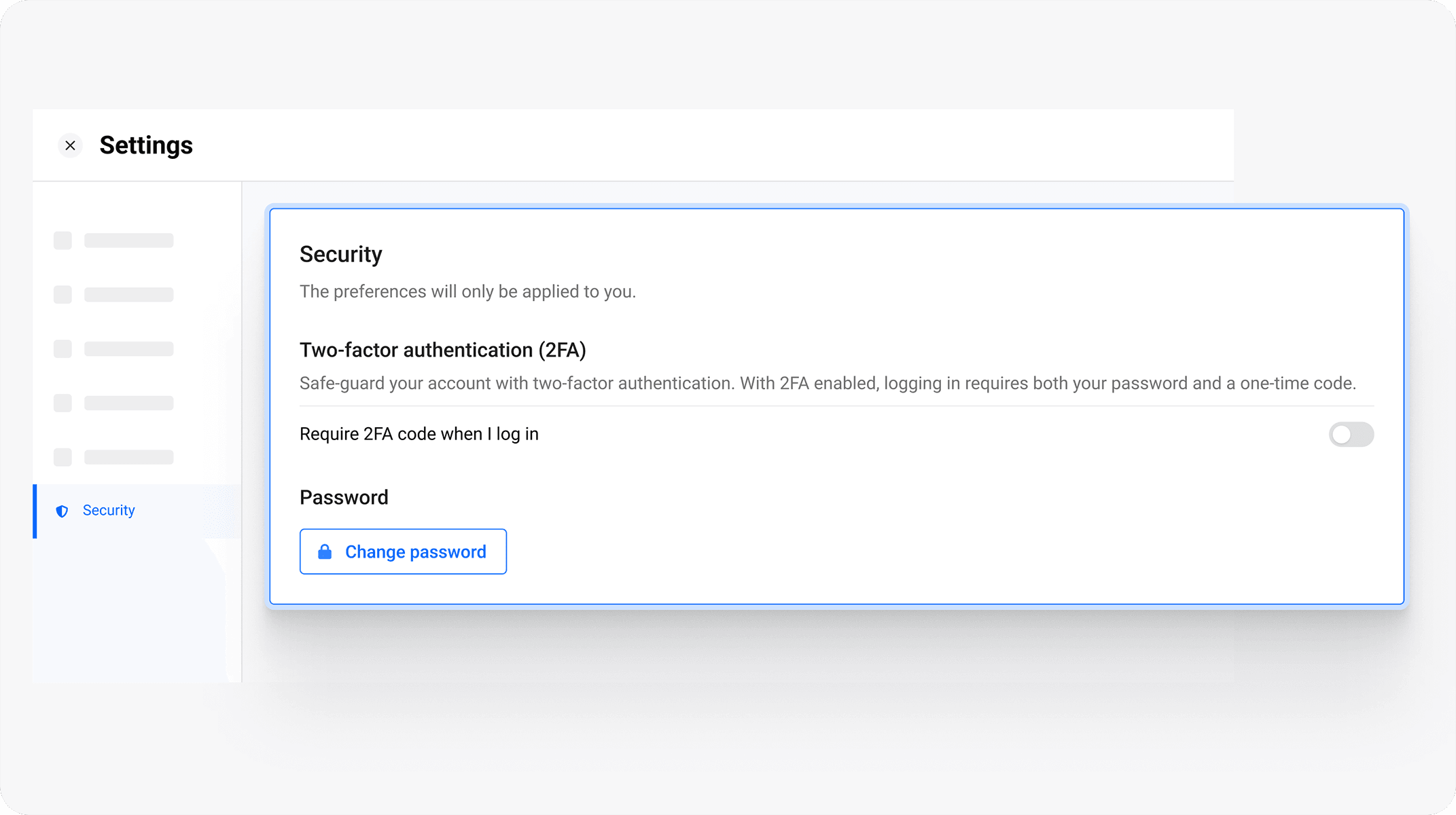
Once enabled, every login will require both your password and a verification code sent to your email.
If You Receive a Code You Didn’t Request
This is a red flag that should not be ignored. If you receive a verification code without trying to log in, it may indicate that someone already has your password and is attempting to access your account.
In that case, we recommend performing the following steps.
- Change your password immediately (use a strong, unique one).
- Check the security of your email account.
- Never share the code with anyone.
- Contact MGID support if anything looks suspicious.
Conclusion
Passwords alone are no longer enough to protect your accounts. They can be leaked, reused or stolen, often without your knowledge.
Two-factor authentication adds a second layer that makes the majority of these attacks ineffective. While it doesn’t make you invulnerable, it does dramatically reduce your risk.
The key is to use it right: choose a stronger method when possible, secure your email account and set up backup access.
The difference is noticeable. With only a password, one mistake can cost you your account. With 2FA, attackers need much more and usually fail.
If you haven’t enabled 2FA yet, this is one of the easiest and most effective steps you can take today to protect your data.